Use Cryptocurrency to Resist Government Surveillance
Cryptocurrency spending--when done with care--is effective at resisting government control and surveillance.
Who Should Read This
This blog post is for anyone that is trying to protect their privacy against government surveillance of our consumer behavior. I see no other rational reason anyone should care.
If you are interested in protecting your privacy against companies that spy on our consumer behavior then you should stop reading this article immediately and instead invest in a virtualized debit card service such as privacy.com. A virtualized debit card service will make it more difficult for other companies to monitor your spending behavior. Virtualized debit cards are also much easier to use and allow you to put in any name and billing address you wish. However your bank and the government will still be able to monitor all of your spending habits.
Why Some People Are Concerned With Government Surveillance
Throughout history governments have abused their power to spy on their citizens to get rid of anyone they do not like. Kings used to search and seize people’s assets at will. The Founders of the United States were aware of this. At the insistence of the Anti-Federalists the Fourth Amendment was made to protect US citizens from unreasonable search and seizure.
In the 20th century governments such as the Russian secret police spied on people before convicting them of “crimes against the state” and sending them to gulags—which were Russian concentration camps. Many met their deaths under these harsh conditions. In many cases the government would make up crimes as they collected data on people they did not like. As Bruce Schneier pointed out Laventry Beria—the architect behind the KGB police—said “show me the person and I will show you the crime”.
Today governments including those of the Five Eyes Alliance all spy on each other’s citizens and share their surveillance data with each other. China and Russia are both infamous for spying on their own citizens. In China the Chinese Government exploits Domain Name System to spy on the traffic of their citizens—even censoring content that should be legal under Chinese law. To help circumvent these restrictions a citizen may wish to subscribe to a privacy-respecting VPN such as Mullvad. But of course the citizen cannot just pay in fiat currency. A good substitute would be a privacy-respecting currency such as Monero
So for those of you concerned about the government spying on your spending habits I assume you live in a country that has abused its powers to censor, spy, and discriminate against people they do not like--and one way governments do that is by monitoring the Internet Activity of their citizens. This article is for these people that are trying to protect their privacy online.
I assume you are not in a life-threatening situation—in which case you should not even be on the Internet nor reading this in the first place.
Why Was Cryptocurrency Invented?
Let me start with why cryptocurrency was invented.
Cryptocurrency was invented in 2008 by an unknown author of the “Bitcoin Whitepaper”. Whoever the author(s) of this whitepaper were were frustrated with the cause and outcome of the 2008 Global Recession. During the 2008 Global Recession, US housing and lending markets crashed--causing a global bank panic. Real banks failed. The FDIC had to step in and replenish people’s money. Unsurprisingly, people lost faith in the health of the market, and people stopped paying for goods and services as much as they normally did. Since the US has a massive influence on international banking, this has caused financial issues for many around the world.
When bank panics like this the US prints more money and grants it to banks first. The US Federal Government does this in the hope that banks will lend more--stimulating economic growth. Unfortunately, banks still did not lend as much as the US Government hoped in the Great Recession. Without money being granted to people as an investment, money cannot be easily spent to help the economy grow. This causes more money to circulate. The easier it is for a person to obtain money,, the less valuable the money. Even if $1 USD remains $1 USD you will find yourself being able to buy fewer items with it as prices rise. This is a social event known as inflation. Consider the price of gas in 1920 vs 2026:
As we can see modern gas prices are drastically higher than they were 100 years ago--in fact modern gas prices are over 10X more expensive today than back in 1926! If such a sharp rise took place in a few years it would ruin the US economy beyond repair. But since it happened gradually the damage is less severe.
The creator(s) of Bitcoin were tired of how federal governments and banks hack financial systems in their favor at the expense of the public. They believed that a peer-to-peer online system of payments where payments did not need to be verified by a “central authority” like a bank would be a solution to the problem.
How Bitcoin Works
Bitcoin was designed to be treated as “digital gold”. If the creators wanted Bitcoin to be treated as a precious metal why did they not recommend people to just use precious metals as currency. Well, even the prices of precious metals are manipulated by centralized authorities. The creator(s) hoped Bitcoin’s design would make it resistant to that. To do this Bitcoin was designed to only allow a finite hard-limit of 21 million coins total in circulation. To prevent people from counterfeiting Bitcoin each Bitcoin payment must be verified by a community of paid volunteers known as “Bitcoin nodes”. These nodes had a machine, or rented computing resources, to verify if a Bitcoin payment was valid. To verify each submitted Bitcoin payment a paid volunteer, which can also be an owner of a Bitcoin node, must solve a math puzzle that is believed to be difficult to solve. It is our faith in the difficulty of solving this puzzle, the Nakomoto Consensus Algorithm.
The Nakomoto Consensus Algorithm: What Makes Bitcoin Payments Faithful
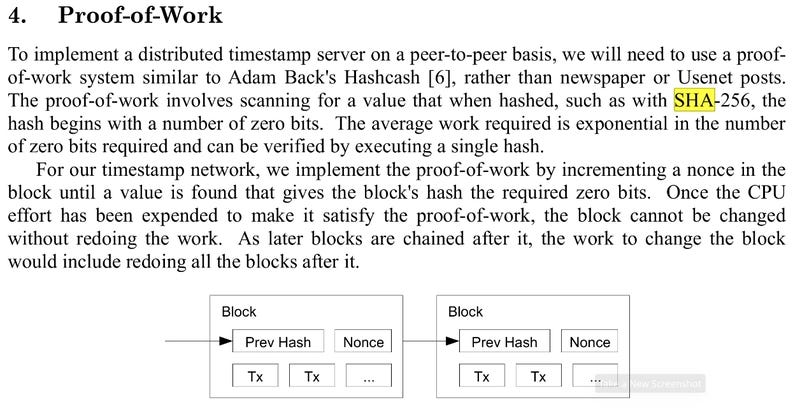
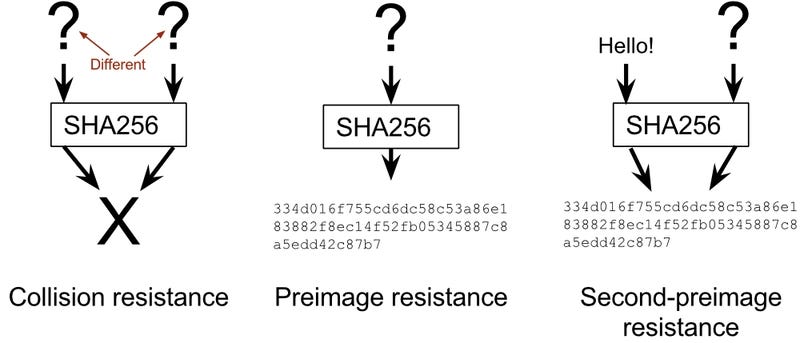
To solve this puzzle a miner must guess a random number, or nonce. The nonce must be appended to the payment information. Next the payment information, including the nonce, is applied to a mathematical function that prints an identification number that is unique to the payment. It must be difficult for people to predict what input produced a known identification number--a concept known as preimage resistance. It must also be difficult to find a second distinct input that produces the same known identification number--a concept known as collision resistance.
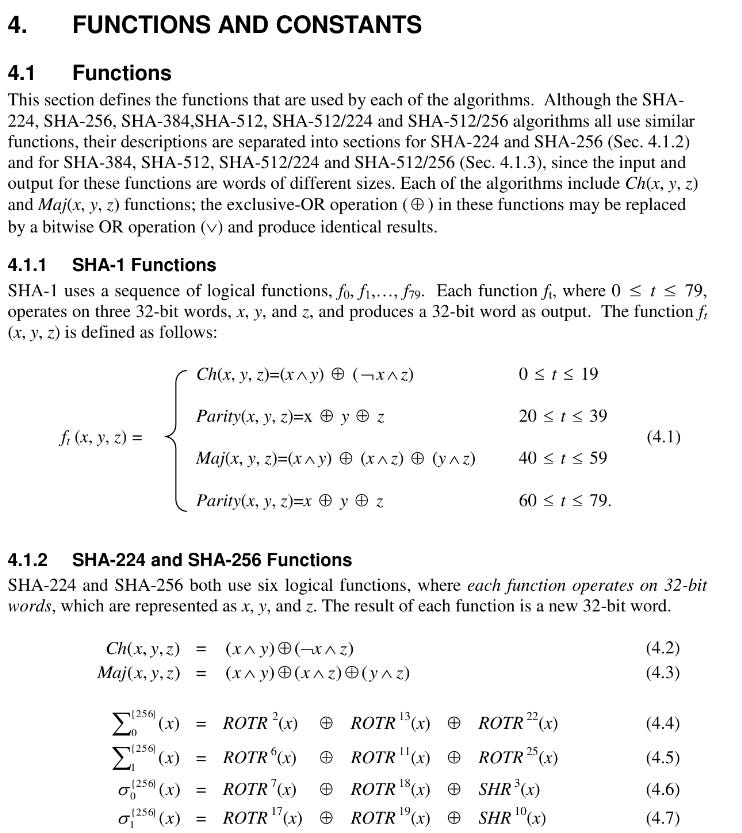
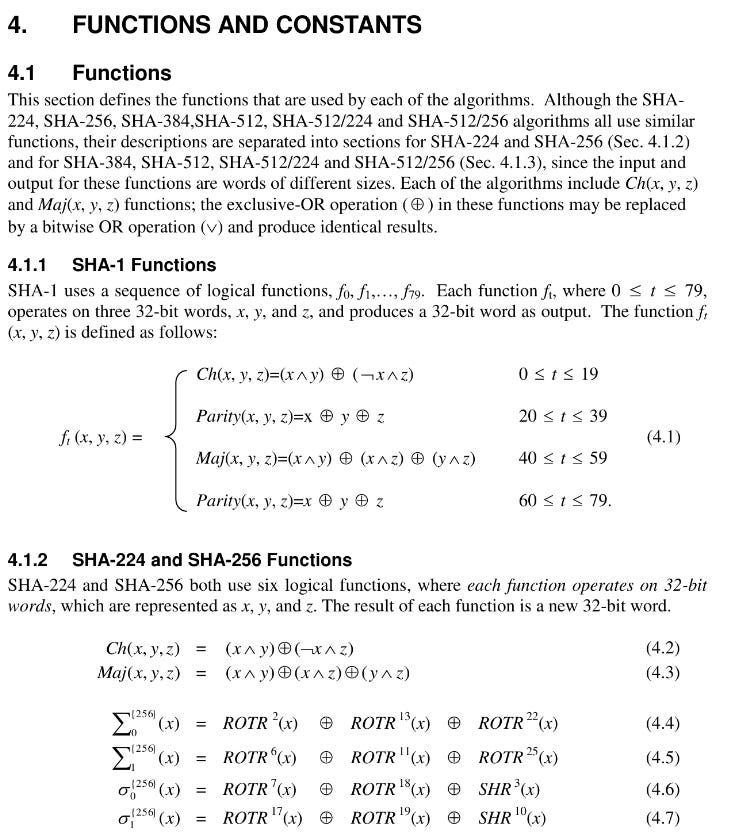
With these properties it would be difficult for attackers to make up payment information that solves the Nakomoto Consensus puzzle. Had this been the case people would be able to write programs that can solve the Nakomoto puzzle in mass-number--destroying faith in Bitcoin’s ability to avoid counterfeit coins. Although Bitcoin was meant to resist government influence it is ironic the creator(s) of Bitcoin have chosen to use mathematical functions to protect financial secrets standardized by the US Federal Government--known as cryptographic algorithms. The cryptographic algorithm, known as SHA-256--a message digest algorithm--was designed by the National Security Agency--an organization that real American citizens have criticized for spying on people around the world, including American citizens.
The US Federal Government’s Unintended Role in Bitcoin’s Creation
Why would the Bitcoin creator(s) use cryptographic functions to protect secrets that were made by a federal government--the very entity they are trying to protect influence from? Why would they trust an organization infamous for spying on their own people behind their back?!!
The answer is that the US Federal Government has released the designs of these algorithms to the public--welcoming scrutiny from academic professionals around the world.
After the academic community released attacks against earlier versions of SHA-256--the NSA released SHA-256 to be resistant to said attacks. To this day researchers conclude SHA-256 continues to be resistant to attack. The US standardizes its cryptographic algorithms under the Federal Information Processing Standard (FIPS).
As I mentioned earlier, SHA-256’s main property is preimage resistance. Collision resistance is also important--the idea that it is difficult to find two distinct documents that map to the same SHA-256 hash output. A third important property is that it is difficult to find a second distinct document that maps to a known hash output of a known first document. Below are diagrams to help you understand these concepts:
If you want to learn more about which US Federal Government cryptography was used in Bitcoin’s design, I would strongly recommend “Serious Cryptography: 2nd Edition” by Jeanne-Phillipe Aumasson.
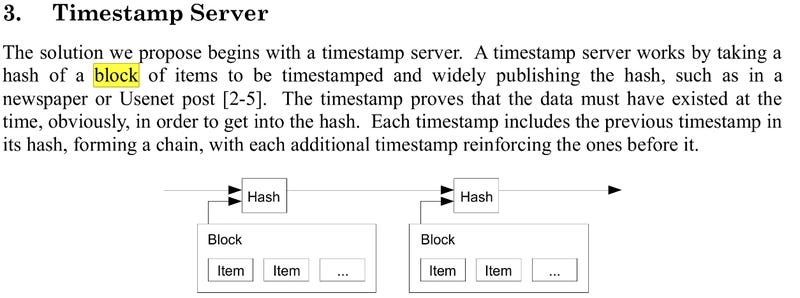
Let’s go back to the Nakamoto Consensus Algorithm. I just explained why SHA-256 is trustworthy. I also explained payments are hashed such that the last several number of required digits is zero. The brilliance of this system is that for each extra trailing zero required the miner has to make twice the number of guesses to solve the puzzle! Bitcoin was designed to scale the number of trailing zeroes required as more miners participated--requiring the puzzle to get harder to solve to avoid counterfeiting coins.
Once a miner solves a puzzle and presents the solution owners of Bitcoin full nodes verify the solution is correct. To verify the solution is correct a full node simply rehashes the payment information, checks that the SHA-256 hash matches the proposed hash the miner has pledged solves the puzzle, and double-checks the SHA-256 hash has the required number of trailing zeroes. Once all of this is verified the Bitcoin payment is considered valid. As long as 2/3 of nodes acknowledge the payment as valid it is difficult for the attacker to trick the public into thinking a payment is invalid.
Simply verifying each payment is not enough. Since money’s nature is to pass from one person to another, a complete record of each and every coin’s history traveling from one person to another must be recorded to not lose coins on the network. Such a record is known as a ledger.
This immediately brings forth a new problem--how do you stop people from tampering the ledger! Imagine if someone simply reassigns the destination addresses for payments. If that happens an attacker can steal money from everyone else’s wallet free of charge! To prevent this Bitcoin enforces a rule that only the longest chain of verified payments is the true ledger of the Bitcoin network. While finding a solution to the Nakomoto Consensus. To make this hard the previous hash for a set of Bitcoin payments--or block of payments--is actually part of the payload for the currentmost Bitcoin payment block--chaining hashes of payment blocks together (hence why Bitcoin is called a blockchain):
The 51% Attack
With this system the only way to counterfeit Bitcoins is to somehow solve Nakomoto puzzles faster than the entire community of Bitcoin miners. And to do that an attacker needs to hijack enough Bitcoin mining machines to control more than 50% of the hashing.
There are two reasons why this is going to be very hard:
1. The global hash rate for Bitcoin is massive.
2. Anyone with access to a machine’s computing resources can participate in mining. Remember access to machines is controlled by authentication and authorization (to varying degrees of success!)
To give you an idea of just how hard that is here is the current global Bitcoin hashrate as of April 25, 2026:
As the chart above makes clear the Bitcoin global hash rate is rising exponentially with time--a testament to the durability of the Nakamoto consensus algorithm.
One zettahash/second is equal to 10^21 Nakamoto puzzle solutions/second. Good luck compromising enough machines to hijack the chain!
How 51% Attacks Allow Double-Spending
Once you compromise enough machines, you can fork the Bitcoin blockchain and start forging your own Bitcoin payments to a limited degree. In double-spending the attacker spends the same Bitcoin that was at first spent on the original Bitcoin blockchain elsewhere.
During a 51% Attack the attacker’s fork becomes the new longest chain--therefore the original Bitcoin payment the attacker made becomes null-and-void. The new Bitcoin payment the attacker made is what is considered valid. The attacker can also deny confirming others’ in-progress transactions--a denial of service on the Bitcoin blockchain. If the attacker wishes they can try to deny as many transactions as possible--rendering the Bitcoin network useless as a means of payment.
What 51% Attacks Cannot Do
You cannot do the following with a 51% Attack:
1. Mint coins without limit. The attacker cannot violate the 21-million hard-limit since that is the consensus amongst owners of Bitcoin Core full nodes. To circumvent that the attacker will have to next hijack control over majority of full nodes. Still, the attacker can assign newly minted coins to the attacker’s own wallet before the 21 million limit is reached.
2. Steal coins from others’ wallets. Without knowledge of the private key the attacker cannot steal your coins even with an active 51% attack.
3. The older a transaction is the harder it will be for the attacker to reverse the transaction. This is why multiple confirmations reduce a payment’s vulnerability to 51% Attack.
Private Keys: Safeguarding Your Net Worth
Bitcoin is built-on public-key cryptography. In the case of Bitcoin that means you--the Bitcoin owner--is responsible for keeping a large number a secret. That secret is your Bitcoin private key. You *never* share it with anyone--not your family nor your friends nor your cryptocurrency exchange nor bank. If anyone learns what your Bitcoin private key is they can spend your Bitcoins without your permission--even if they did not also steal your Bitcoin wallet--regardless of whatever form it is in (software or hardware wallet it does not matter). Storing the private key has been a difficult social problem. In the past real people lost massive amounts of cryptocurrency from recklessness, compromise of one’s wallet (they probably used a hot wallet--a cryptocurrency wallet that has Internet Access), or even from real 51% Attacks (easier to attack smaller cryptocurrency networks than larger ones).
One of the best ways to protect your private key is to use a cold hardware wallet. This is a dedicated computer that stores the private key using specialized hardware to protect the key from malware. And I will soon discuss why the OneKey Classic 1S and more so the OneKey Pro is a viable option.
Benefits of Cryptocurrency Use
Private Spending
Professor Shoshana Zuboff from Harvard University wrote an excellent book titled ”The Age of Surveillance Capitalism”. In her work she argued online payments made it possible for businesses and governments to monitor a consumer’s behavior. This is why companies and governments can predict your future consumer behavior and manipulate it: they can see what you are spending on.
On the Internet you will hear common promises that “Bitcoin payments are anonymous”. I am sorry to tell you that simply using cryptocurrency alone does not guarantee that payments are either anonymous or private.
The good news is that there is a way to do it but you will have to work harder than the average online spender to protect your privacy. I will discuss how to spend cryptocurrency privately to protect your consumer behavior much later in this article.
Profit from Cryptocurrency Trading
If you have already heard of cryptocurrency there is a very good chance someone taught you can make money trading one cryptocurrency for another. The trick is doing this in such a way where you trade for low-value coins that become more valuable in the near future. The metal you receive will be worth much more than the one you gave away in the future--making you richer!
Take a look at the following chart:
Since Ethereum grew in price faster than Bitcoin. If in 2016 you traded $100 USD worth of Bitcoin for $100 ETH (assume no financial loss from transaction and exchange fees) you would have ~$130,000 USD worth of ETH in 2026!
This is why people are motivated to trade cryptocurrency coins--treating them like trading precious metals.
If you are interested in learning how to trade cryptocurrency as an investment I would strongly recommend Glen Goodman’s book "Crypto Trading”. In his book Goodman argues one should learn Technical Analysis to profit from cryptocurrency trading--simply holding does not pay--trading wisely does.
How to Purchase Cryptocurrency
There are several good options to purchase cryptocurrency. The most convenient is purchasing from a centralized cryptocurrency exchange. These are websites owned by companies that allow one to trade cryptocurrency any time of day on-demand. Many of these exchanges even have API services to allow one to trade using computer programs--program wisely!
If you are a beginner I would recommend making an account with the Kraken cryptocurrency exchange first. I found this cryptocurrency exchange to have the best options to safeguard your account from thieves--including support for strong Multi-Factor Authentication using Universal Second Factor Authentication.
If you are using a cryptocurrency exchange I would strongly encourage finding one that offers the option to protect one’s account with Universal Second Factor Authentication. I would also recommend one check if the website for the exchange is protected under Domain Name Systems Security Extensions--this will ensure that an attacker does not redirect you to the attacker’s site even if you type in the domain correctly. Kraken offers both.
Kraken even offers the ability to receive Pretty Good Privacy emails--this will help you tell if anyone sends you a phishing email in Kraken’s name. If that happens someone can steal your Kraken login credentials by tricking you to visit the attacker’s website instead of Kraken’s real website.
Finally Kraken is one of the few exchanges that offers the purchase and sale of Monero (the best privacy-protecting cryptocurrency at the time of this writing)--combined this is one of the best exchanges that can help protect your privacy. I will talk more on how to do that soon.
Why Use a Cold (Offline) Hardware Wallet To Store Your Cryptocurrency
As I mentioned earlier a hardware wallet is the best way to protect your cryptocurrency assets from thieves. Certainly there are several software such as [Electrum](electrum.org) and even wallets on cryptocurrency exchange websites. Allow me to say this: the easier it is to access a wallet from the outside public Internet the sooner someone will try to steal it! Cryptocurrency is valuable and there are countless tales of people stealing them--such as from North Korean hackers.
I would never store cryptocurrency in a software wallet offered by an online exchange--those are most often hacked due to a software bug. The Chainalysis article I hyperlinked earlier makes that clear. What is astonishing is that even though these online services store their assets using hardware wallets attackers figure out a way to gain access to the assets stored in them. This is why it is not good enough to store your private key in just a hardware wallet. You must store it offline--not connected to a computer in any sense of the word when not in use. You will lose money if you do that for too long without withdrawing to a cold, hardware wallet. A mobile wallet is also a terrible idea--even if it stores the private key directly on your mobile phone. Your mobile phone is your second best attack vector after a browser extension--and it therefore should come as no surprise that mobile wallets are yet another hot target for cryptocurrency theft.
This is why you use a cryptocurrency hardware wallet such as OneKey.
Get Started with OneKey Classic 1S
OneKey is one of several cryptocurrency hardware wallets that I recommend here for beginners to cryptocurrency.
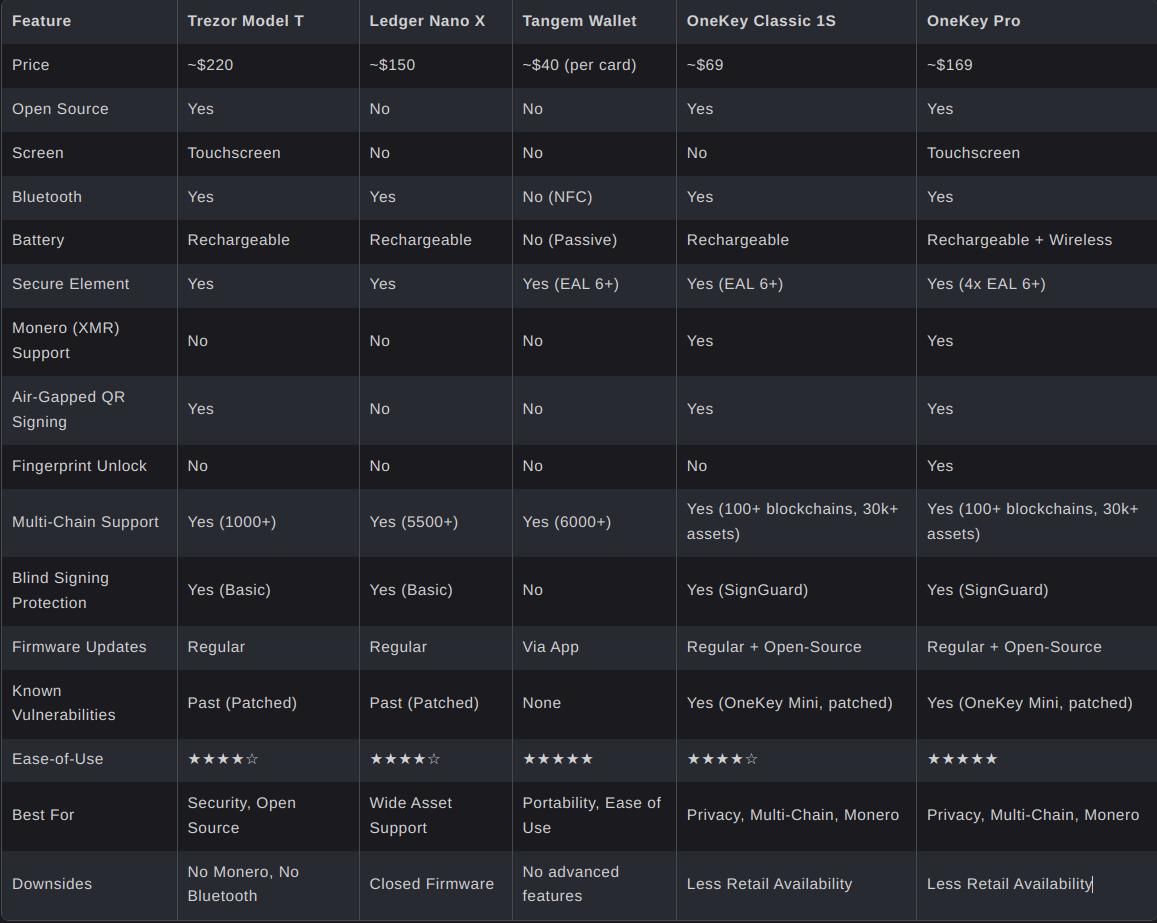
Below is a chart comparing the features of each major cryptocurrency hardware wallet.
How the Cold Hardware Wallets Compare
So let me guide you through the pros and cons of each wallet.
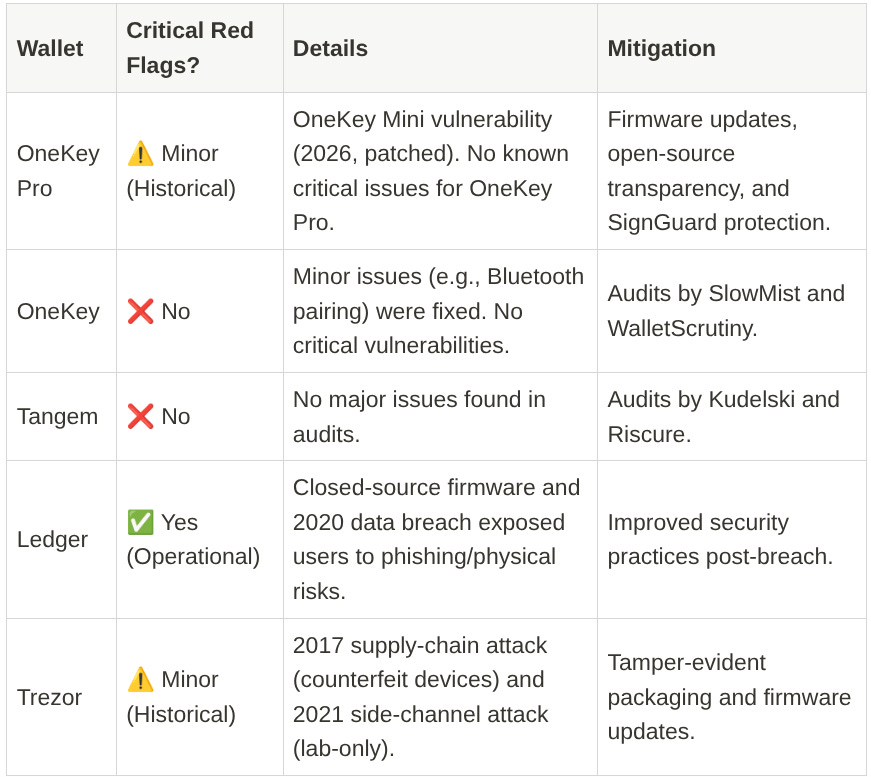
Audits: The First Thing You Look For
How do you know the software the cold hardware wallet ships with is safe? An audit by an independent third-party with reports of low risk is a good sign that is the case.
Let me start with OneKey Classic 1S. This wallet has been audited by WalletScrutiny in 2025--passing all 10 tests. It also has been audited by SlowMist by January 2024.
With all fairness all the other cold hardware wallets have been audited by independent third-party companies.
Heuristic Security: Did The Cold Wallet Survive Battle?
However not all of these hardware wallets are equal in protecting their users against the wild.
Here is table summarizing real incidents that took place against each wallet:
As we can see OneKey and Tangem faced the least problems in production for consumers.
It makes sense to next spend the time comparing OneKey and Tangem:
Tangem vs OneKey
I personally believed the following link was an excellent comparison vs Tangem and OneKey.
So Tangem, unlike OneKey, is a cold hardware wallet that stores the private key in what looks like a credit card. Like all other cold hardware wallets it has a Secure Element--a specialized microprocessor designed to be resistant to software-based attacks, cloning, or extraction of the key.
Unlike all the other cold hardware wallets it has the comparative advantage of being resistant to wireless and wired attacks. There is a downside to this: the user must install Tangem’s mobile wallet to use the Tangem key card. The issue with that is an attacker can trick users into downloadin phishing mobile apps.
This is what happened with Ledger victims in 2020. In 2020 hackers confiscated the emails of thousands of Ledger users. They next sent emails asking victims to download phishing apps of Ledger Live. Ledger Live is supposed to be the official mobile wallet app for Ledger. The attackers tricked victims to download the attackers’ fake version of Ledger Live.
This is one of the reasons why I insist with using verified desktop apps--especially if the cold hardware wallet vendor’s website allows one to download the desktop app directly--which Onekey does.
Since OneKey’s website--like many other cryptocurrency vendors--is protected under Domain Name Systems Security Extensions and HTTPS--we have reliable assurance that the desktop wallet we download is the true wallet software published by OneKey.
But what about making sure the copy of the wallet software binary we get is faithful to the source code of the wallet? To verify that we check if the wallet’s source code is open source, or available to the public, and that the binary file is a reproducible build.
Open Source: Assurance The Public Can See the Source Code
Open source software projects publish their source code to be reviewed by the public. There are many licenses such as MIT license or BSD license. Open source is a business strategy to gain customer trust. Both Trezor and OneKey publish their source under open source licenses.
I encourage you to choose privacy products that publish their source code under open source license. I am aware the writers of Building Secure Software admitted just because software is open source does not mean it is more secure--still in principle it is best because it makes it easier for people to find and report security bugs.
Reproducible Builds: How Do You Know the Source Code Matches the Binary
In the real world the source code must often be compiled to a binary executable. A binary executable is a file that is directly executed by your machine’s CPU. It is just a large file of 1s and 0s. The problem with converting source code to binary is that each time one edits the source code the binary file’s contents change too. This is a problem for security because customers need to know the binary executable they are running matches the manufacturer’s.
To verify this manufacturers often post the SHA-256 checksum along with the downloadable binary executable. If it does not then there is a risk the user does not have the correct binary executable. Who compiled the binary? An attacker? A random person on the Internet. Was there a mistake in recording the correct binary version?
I must admit that OneKey Classic 1S fell short of having a reproducible build compared to Trezor Safe 7 here. It would be nice if OneKey Classic 1S had a reproducible build for the latest version.
Backups and Recovery
NEVER backup your Bitcoin private key on a piece of paper, on your computer drive, and definitely not on a sticky note!
Countless people have suffered from cryptocurrency theft by now including The Wolf of Wall Street.
The best way to protect your master secret is to use Shamir Secret Sharing.
In this backup and recovery technique cryptography is used to split up the private key into, say, 3 pieces. Shamir Secret Sharing lets the secret-keeper decide how many pieces the recoverer must have to recover the original secret. For example it can be 2-out-of-3 pieces. It is statistically impossible to guess what the original secret is without having at least 2 pieces in a 2-out-of-3 SSS scheme. Shamir Secret Sharing is also resistant to attack against quantum computers. Which is awesome!
Its just that it is hard to find a cold hardware wallet that supports Shamir Secret Sharing. Trezor is the only one that does. Unfortunately, that’s the case--Shamir Secret Sharing is the backup method most resistant to theft, loss, and collusion (people entrusted with a Shamir share betray you).
How to Safely Pass On Your Crypto Assets to Your Inheritors With Shamir Secret Sharing
If you are concerned about passing on your cryptocurrency assets after your death--Shamir Secret Sharing is the most reliable way to do it--and I would encourage you to invest in Trezor’s Safe 7) wallet for that reason.
Do this: purchase two Trezor. Yes that’s $200 USD but its worth it for what I am about to tell you. Next go to your Trezor wallet and setup 2-out-of-3 Shamir Secret Sharing. Store two pieces--one each in one metal share. The third and final Shamir Secret Sharing piece should be stored in an offline password manager such as KeePassXC.
The one and only piece in your password manager is safe from everyone--including your family and friends who will most likely steal it if given the chance (be careful of your in-laws [No seriously be careful!]).
Once you die the Shamir secret in your password manager is inaccessible to everyone--safe from everyone though. This is where the next two physical shards from Trezor are important.
Entrust one physical piece with you and your family--such as in your family home. Place it in a safe place--the same safe place you place your family’s goverment-issued Identification documents.
A thief would have to be brave enough to threaten your family at gun point for both your Shamir secret and the one in your house. Either way law enforcement would have just reason to pursue the criminal. Today it is hard to get away with theft of cryptocurrency. Firms such as Chainalysis and Elliptic exist to help law enforcement catch criminals--and they have in the past.
Still, you should not just store two physical Trezor shards in your family’s possession--or they can steal your cryptocurrency behind your back!
So the third and final Trezor shard can be entrusted to a bank. Write in your legal will that upon your death the bank is supposed to release the third physical Trezor shard to your family.
This means the government does have access to one physical shard though. The US Constitution’s Fourth Amendment guards one’s family against unreasonable search and seizures--and the US Government will technically have to file a search warrant before they can confiscate such an item from a tax-paying home.
This is the best method I can think of to guard one’s assets even after one’s death to ensure it is safely passed to one’s family as inheritance.
In the Event One Shard is Stolen or Lost
In the event one shard is known or suspected to have been stolen you the user can rotate the Shamir Secret in time to resolve the matter. In such a case one would have to move one’s cryptocurrency assets to a new wallet under a new Master Private Key and regenerate all shards. Still this will nullify the one stolen shard.
If one shard or more shards have been destroyed the user can regenerate a new set of shards with the same Master Private Key.
My Two Top Picks: Trezor Safe 7 for Advanced Users and OneKey for Novices
So in conclusion I would advise newcomers to start with OneKey Classic 1S. It is much more user-friendly than Trezor, has no history of breaches (so the user does not have to work hard to protect themselves), but has weaker security protections.
Trezor Safe 7 is for more experienced users that took the time to study the risks and benefits of blockchain technology and modern cryptography. Such a user should be educated in both computer security principles as well as have had extensive experience with using cryptocurrency with others. Only Trezor offers Shamir Secret Sharing. Still be warned that in 2017 counterfeit devices were a problem.
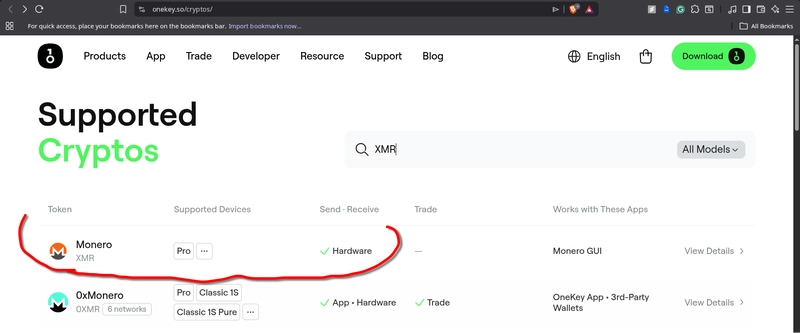
OneKey Pro is the absolute best cold hardware wallet to protect the privacy of one’s payments--it is the only one that allows one to use Monero, has no history of critical vulnerabilities, and is easy to use. It is the most expensive though. Unlike OneKey Classic 1S the OneKey Pro has proper reproducible builds.
For both of the above wallets I would strongly recommend downloading the desktop app for either whichever you choose. Even bookmark the website pages so you do not fall for phishing scams. Trezor’s website is fully protected under DNSSEC so it will be resistant to a DNS Cache Poisoning Attack. This can direct you to the attacker’s site even if you bookmark the correct domain. OneKey’s website on the other hand is not fully signed under DNSSEC so it does not offer the same protection.
Although this is not a deal breaker it is a cause of concern. Without full protection under DNSSEC visitors to OneKey do not have reliable assurance they are visiting the true server owned by OneKey. It could be an attacker’s behind the scenes without the user knowing in the event of a DNS Cache Poisoning Attack. This is why most banks and cryptocurrency exchange/vendors go through the effort to ensure their website domains are fully protected under DNSSEC: visitors are vulnerable to phishing without it.
I refuse to recommend Ledger since its technology has been hacked and is proprietary.
I refuse to recommend Tangem even though it has no confirmed history of breach since it is too difficult for me to use (I will not use NFC with a specific mobile phone app I demand the freedom to use third-party apps on any platform in case my current top choice wallet gets compromised). Also keep in mind that having to rely on the mobile app makes one susceptible to the same phishing mobile app issue Ledger Live faced in 2020.
Not Your Node Not Your Rules
In the world of blockchain there are three golden rules that govern one’s ownership of their cryptocurrency:
1. Not your key not your coins. This is why I strongly recommend a cold hardware wallet. It is impractical for malware to get to the cold hardware wallet. Also you can backup the key with Shamir Secret Sharing with Trezor.
2. Not your node not your rules. I will discuss the underrated importance of using one’s own full node here.
3. Not your hardware not your data. In legal jurisdictions everywhere the physical location of the hardware determines ownership. Remember that!
I would like to say this: you should be using your own full node on your own local machine whenever possible. Having your own full node guarantees your transaction is not denied by another node that enforces its own rulesets. Earlier in this article I explained all Bitcoin Core Full Nodes follow the same standard set of rules ( and the same logic applies to all other cryptocurrency networks). So how is that possible? Well, most full nodes owned by companies are accessible only if you are a registered user that have signed the terms and services--so they can deny your transaction through your web interface even though their full node follows the standard protocol for payment confirmation!
A company’s full node can even forcibly switch your newcoming transactions onto a new blockchain without your approval! This is called Chain Hijacking.
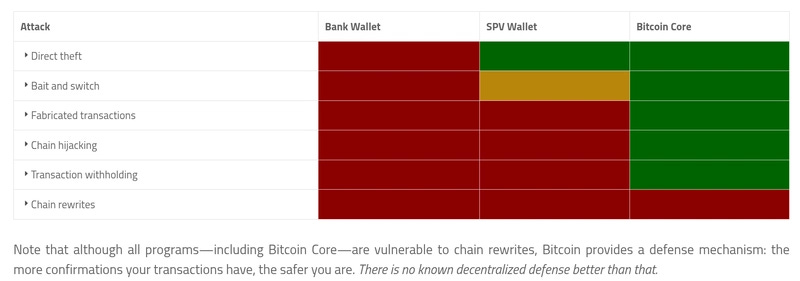
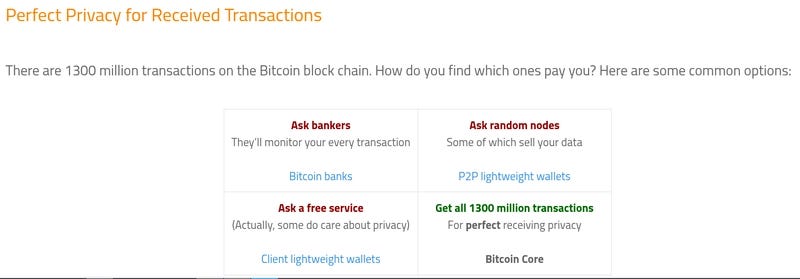
Another reason you should use a full node is to protect you from fraudulence. As a merchant you should be using your very own full node in your physical possession to guard you against fraudulent transactions. Bitcoin.org gave an excellent article comparing the benefits of how a full node guards against fraudulent transactions compared to relying on someone else’s.
Just see how well Bitcoin Core guards your privacy compared to any other option:
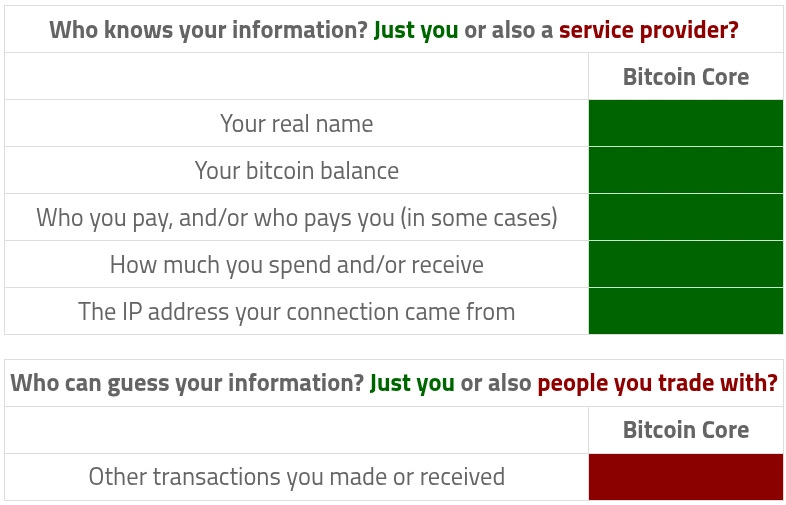
Also when you use your own full node on your own local machine only you know the information sent to your full node. Your full node will not resend your personal details to third-party nodes (except your IP Address). Here is the chart by Bitcoin.org that displays this:
Again I would like to stress that even your own localhosted full node will pass its IP address to third-party nodes so it is wise to use a privacy-respecting VPN such as Mullvad as I do when you do.
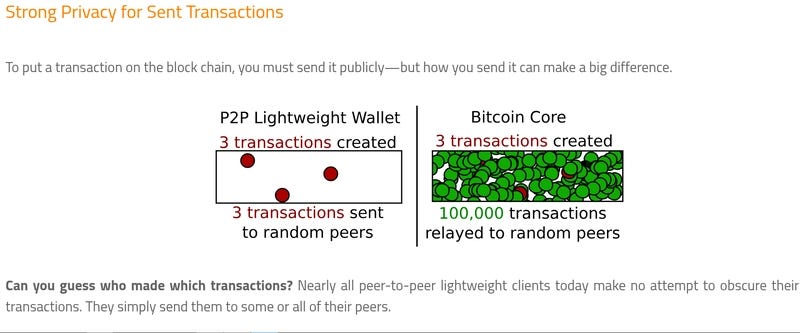
As these diagrams make clear it is impractical for anyone to figure out which transaction was yours when your own full node is broadcasting literally all transactions performed throughout the world to other full nodes! This is a case of information-theoretic privacy.
It is amazing how much a full node can guard you against a cheating customer as well as protect your privacy. Local hosted full nodes do not get the recognition they deserve.
The only attack a full node cannot defend against is the chain rewrite attack (51% Attack). To combat this blockchains do multiple confirmations of blocks to make it harder for such attackers to reverse transactions.
Coins Worth Owning
There are only three coins I truly care about:
1. Bitcoin: So much excellent documentation has been written on Bitcoin’s technology that that reason alone is worth taking the time to learn and use Bitcoin. Once a cryptocurrency newcomer has experience with Bitcoin it is much easier to learn how to use the others. If you are new to cryptography I strongly encourage you to read “Serious Cryptography” by Jeanne Phillipe Aumasson. I would also recommend ”Understanding Cryptography” Second Edition by Paar and Pelzl. These books will equip you to understand the technology Bitcoin was built on (which were US Federal Government approved cryptosystems). This is a prerequisite to make educated decisions for yourself on how blockchain technology will help you in your privacy needs.
2. Monero: The only cryptocurrency that truly kept its promise in guaranteeing private payments. Earlier I mentioned Professor Shoshana Zuboff in her work
”The Age of Surveillance Capitalism” argued our online consumer activity can easily be traced when we conduct fiat payments. Monero is the first digital currency that is so far untraceable. Unfortunately, this also makes it harder for criminals to be caught. Not that this means Monero should be banned--such criminals would misuse other cryptocurrencies and, more so, physical cash anyway. You can simply withdraw your Monero from Kraken to your own wallet. Be warned OneKey Classic 1S does not support Monero. Only OneKey Pro does.
Not only this but OneKey Pro offers fully reproducible builds.
There are no reports of major hacks against OneKey Pro, offers full reproducible builds, and its UI is great. Its just the most expensive.
For this reason OneKey Pro is the best cold hardware wallet for protecting one’s privacy:
3. Ethereum: The real reason why I am interested in Ethereum is to use stablecoins. The one and only stablecoin I like is DAI. This stablecoin is partially backed by cryptocurrency and partially by fiat--balancing stability of fiat with the government-resistant monetary value that cryptocurrency offers. Stablecoins matter when you are using cryptocurrency in business matters--where you cannot afford a massive drop in price destroying your liquidity or solvency. When conducting business-to-business transactions best you use a stablecoin like DAI!
Cryptocurrency: Its Wins and Fails
Success: Censorship-Resistant
The creator(s) of Bitcoin believed Bitcoin would be censorship-resistant by making Bitcoin a decentralized, peer-to-peer network. This is mostly true. Governments continue to struggle to enforce legal bans of cryptocurrency since it is a decentralized network. Bitcoin can even be bought in decentralized, peer-to-peer exchanges such as Haveno. Still, it is unfortunately much easier to spy on the consumer behavior of Bitcoin payments than the Bitcoin creators anticipated—who claimed participants can be anonymous in the Bitcoin whitepaper.
Failure: Anonymity and Privacy
The only cryptocurrency where it is possible to be private and anonymous is Monero and no other. At the time of this writing the US Federal Government, which owns the most powerful cryptographic code-cracking team on planet Earth, still cannot break Monero’s privacy model.
In the real world most people buy their cryptocurrencies from exchanges that demand users to upload their government-issued identification—which ruins the anonymity and privacy of not only the purchaser and even making it difficult for recipients to protect their privacy and anonymity since coin payment histories are traceable going back to the point in time the coin was minted. Micheal Bazzell, a respected consultant for victims of privacy abuse, has insisted the only universal way to ensure anonymity when using cryptocurrency is by accepting cryptocurrency as a source of payment and then spending the coins from one-time addresses. Convincing people to send you cryptocurrency is not easy as that requires business skills.
Success: Use As A Currency
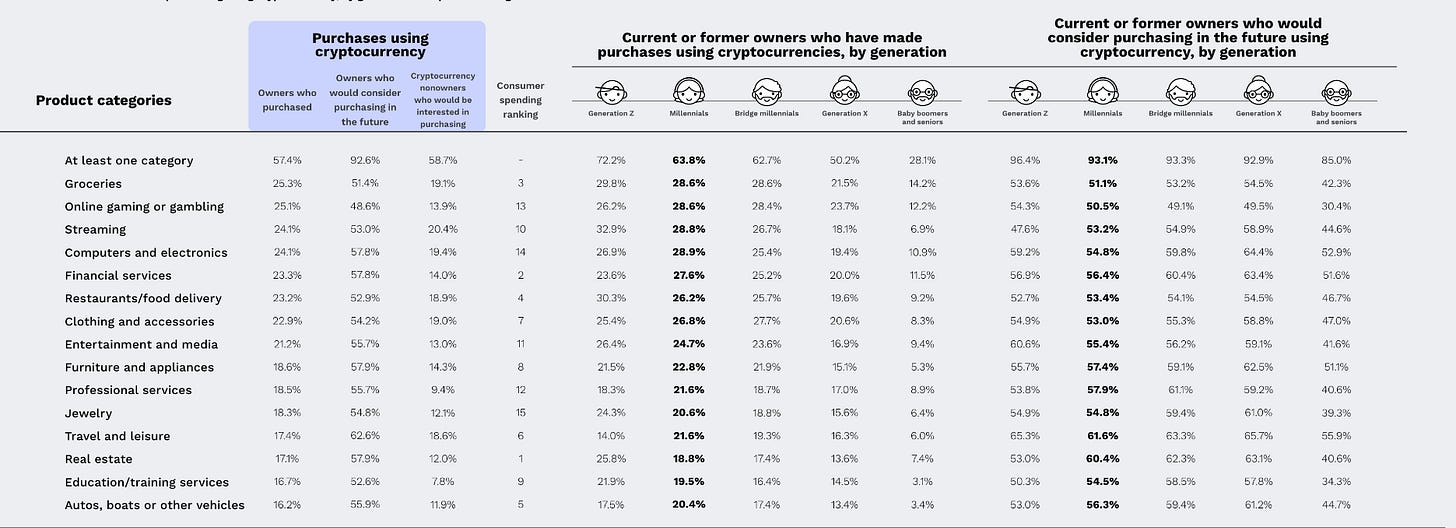
Bitcoin is increasingly succeeding in its mission to be used as a currency. In a 2025 BitPay reports at least 16% of US citizens have used cryptocurrency—where the most common cryptocurrency used is Bitcoin.
The following is a chart of what age group has used cryptocurrency at what frequency from BitPay’s report:
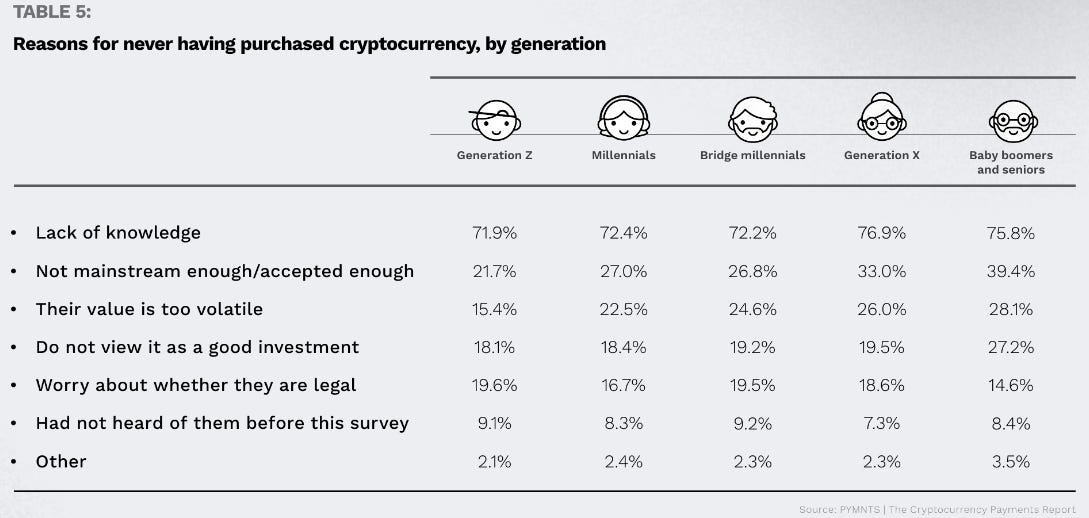
Still, lack of awareness is a huge barrier to entry:
Failure: Decentralization of Mining
Bitcoin and other cryptocurrencies that defend against 51% Attacks force miners to solve computationally-expensive puzzles (a concept called proof-of-work). The Bitcoin inventors intended the Nakamoto Consensus puzzle to be such that the person who succeeded in solving the puzzle would be random.
In the real world this is not the case.
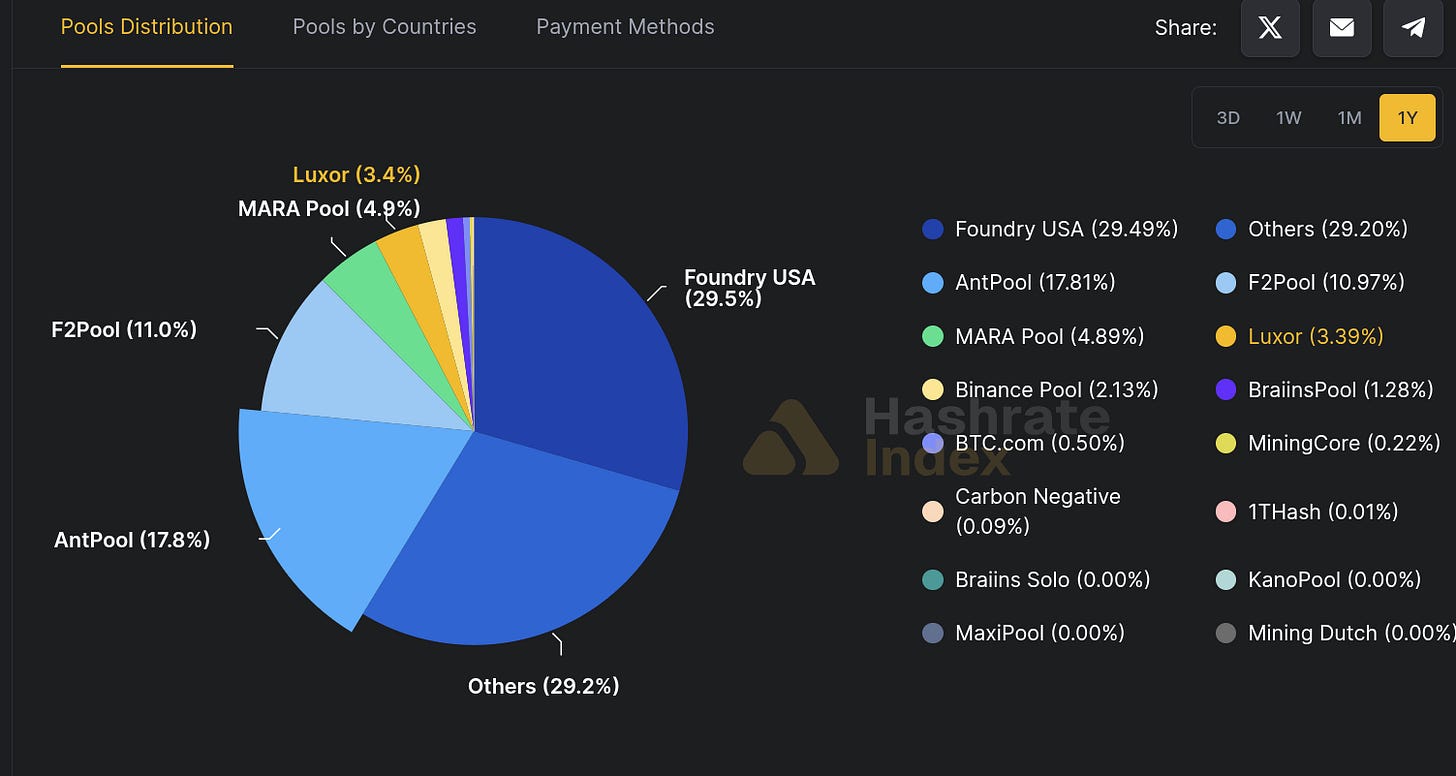
Today Bitcoin miners team up and spread the profits from Bitcoin mining: a system called pool mining.
Here is chart of the centralization of mining for Bitcoin:
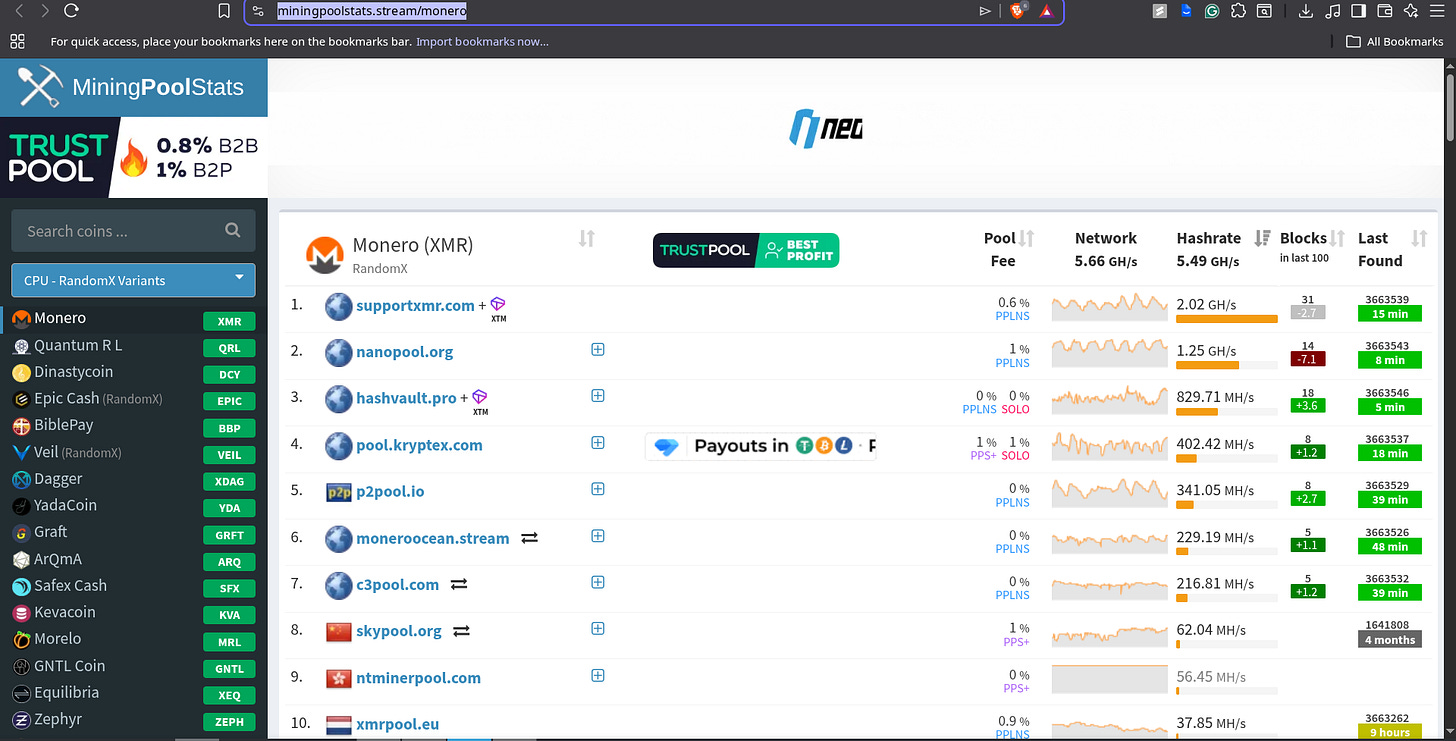
Here is the centralization of mining for Monero:
The situation for Monero is even worse. The top two mining pools for Monero own 59.56% of the global hash rate.
That means if both of the mining pools team up they will possess nearly 2/3rds of the global hash rate. In that case the administrators from both mining pools that have colluded can decide who gets rewarded for minted coins and who does not—effectively becoming the new centralized authority on who gets paid first. Centralization of mining is still an unsolved problem and this is exactly why I don’t recommend storing your entire life-savings in cryptocurrency
Failure: Lack of Insurance
This is cryptocurrency’s worst flaw. In a world that treats cryptocurrency as digital precious metals people have an incentive to store it as an investment—not as a means to hold their life savings. The Gold Standard led to the Great Depression. Since there is no insurance for cryptocurrency and people treat it as digital precious metal there is no reason to disbelieve people will hoard it in desperation in the event of an exchange crash. When cryptocurrency exchanges crash the price of cryptocurrency falls.
The FDIC was invented to gurantee people’s bank balances were protected by the US Federal Government should a bank panic happen. In the world of cryptocurrency the equivalent is an exchange collapse—but there is no insurance against price loss for cryptocurrency! So don’t store your whole net worth as a cryptocurrency—even if you store it as a stablecoin where the price of a stablecoin is pegged to the value of $1 USD!
Conclusion
It is my hope this article serves privacy-conscious readers well should they choose to use cryptocurrencies like Monero to conduct private payments. If you enjoyed this article please let me know your thoughts in the comments. Take care!